An online hotel booking software’s interface, compatibility, integrations, and ease-of-use are elements to look for when upgrading your property’s system. If your hotel is considering ways to increase direct bookings, updating your reservation system can be an excellent tactic, as long as you find a good fit for your hotel. The right hotel booking engine […]
News
Automated Hotel Messages to Guests: Which You Should Be Sending and How
How Investing in Hotel Software Improves Sustainable Hotel Practices
Hotels that want to be competitive and responsible must embrace sustainable hotel practices. But going green doesn’t mean compromising guest experience or operational efficiency. In fact, with the right hotel software, you can achieve both. Smart technology can transform hotel operations while reducing environmental impact. It also helps you avoid greenwashing—saying that your hotel is […]
Hotel Digital Key Trends: What’s Next in Mobile Access Technology?
Hotel digital keys are an essential part of daily operations and the guest stay at an increasing number of hotels. Digital keys offer a streamlined experience, letting guests check-in and get into their rooms, skipping the line at the front desk entirely. Some digital-native hotels are reducing front desk staff entirely in favor of keyless […]
Top 3 Hospitality Trends to Watch in 2025 (And How You Can Stay Ahead)
Technology is continuing to evolve and change the hospitality industry. Staying ahead of emerging trends is crucial to guest experience—and your bottom line. As we move into 2025, there are three major trends that will dominate conversations among hospitality experts and hoteliers. Here’s a glimpse of what’s coming and what you can do to be […]
Let Guests Unlock Their Stay: The Value of Digital Keys In Apple Wallet For Hotels
Hotels that embrace innovative technologies create exceptional guest experiences. There are many reasons why your hotel benefits from having a dedicated mobile app—a key reason being that a mobile app allows a truly frictionless, contactless stay. Imagine this: a guest books a stay at a hotel, checks in remotely through the hotel’s app, and walks […]
What is hotel booking software?
Hotel booking software, also known as hotel reservation software, is any technology that enables hoteliers to accept direct bookings through their website and other direct distribution channels. It is an external interface where guests schedule their stay, choose rooms, and make payments, without contacting the hotel directly. Behind the scenes it manages rates, availability, and […]
The Value of Alternative Payment Options for Hotel Booking Engines
When evaluating a potential hotel booking engine vendor, hotels have many things to balance. First and foremost, core features like real-time integration with key systems. Your booking engine should be designed to convert based on consumer behavior and expectations. Secure payment processing is also a non-negotiable for any booking engine. For more, read: What to Look […]
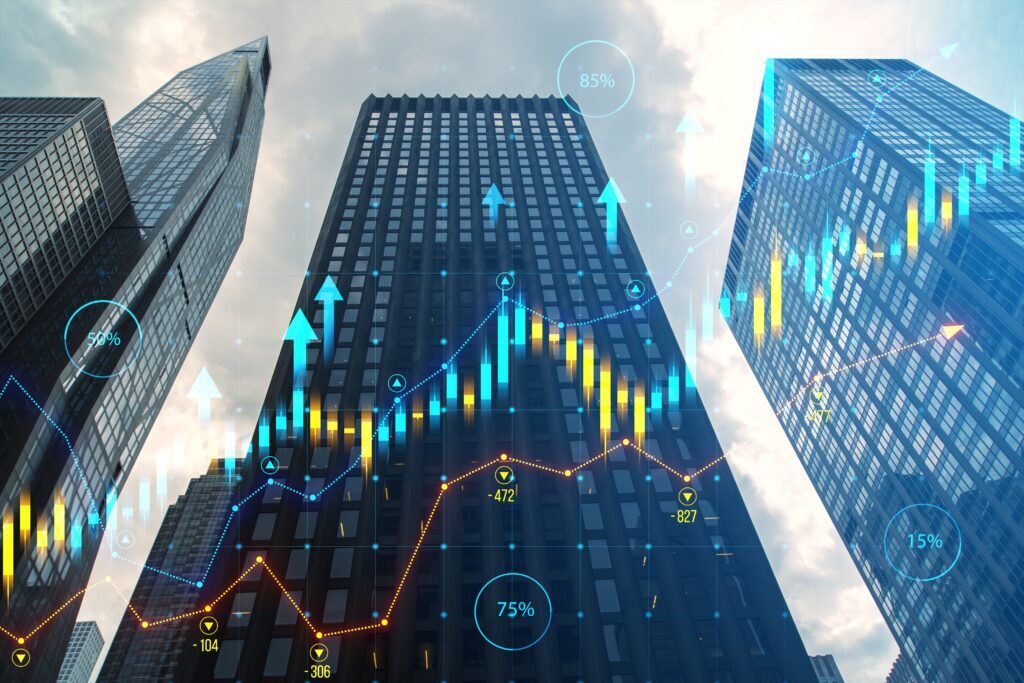
Maximizing Hotel Revenue: How Software Solutions Drive RevPAR Growth
Optimizing Revenue per Available Room (RevPAR) is one of the key focuses of most hoteliers. Travel is up, but so are guest expectations. Navigating the complex world of revenue management requires innovative solutions. While dedicated revenue management software is a component of this process, all of your technology must work together to increase your bottom […]
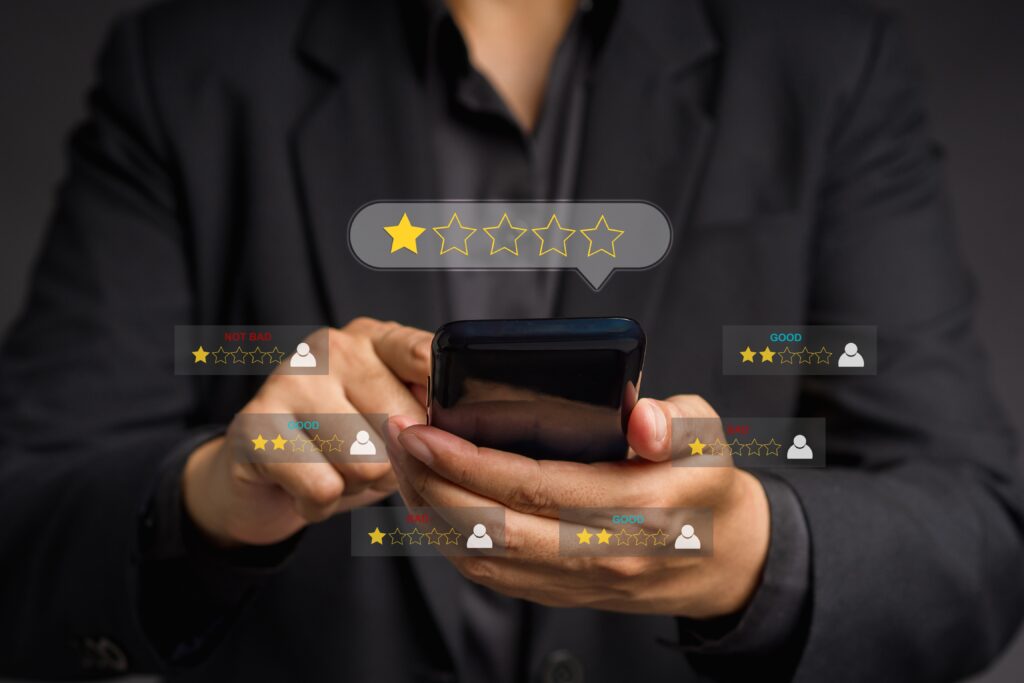
How to Respond to a Negative Hotel Guest Review
Online reviews have an enormous impact on potential guests’ booking decisions. Negative hotel guest reviews significantly impact a property’s reputation and the likelihood a guest will book, or a happy guest will return. According to one study by Brightlocal, 94% of consumers said they avoid businesses with negative reviews. And keeping your overall score high […]
10 Hotel Direct Booking Strategies that Work
There’s no instant way to improve your direct bookings, but these hotel direct. booking strategies combined with our hotel software systems can enhance the guest experience from pre-booking and beyond. Employing our industry-leading technology can provide customer-first, focused tactics to give your hotel the edge over OTAs and third-party sites. Read on to learn four […]
Hotel Email Marketing Examples: 10 Automated Emails Your Hotel Should Be Sending
Hoteliers, the spray and pray approach to email is dead. Start utilizing consumer data to your advantage with triggered, rule-based and segmented email sends. Click below to learn more about the automated emails your hotel should be sending.